Unmatched Robust, Invisible Activity Recording
Operating invisibly, record EVERYTHING your child or your employee does with SpyAgent's wide-array of 50+ computer monitoring features.
Operating invisibly, record EVERYTHING your child or your employee does with SpyAgent's wide-array of 50+ computer monitoring features.
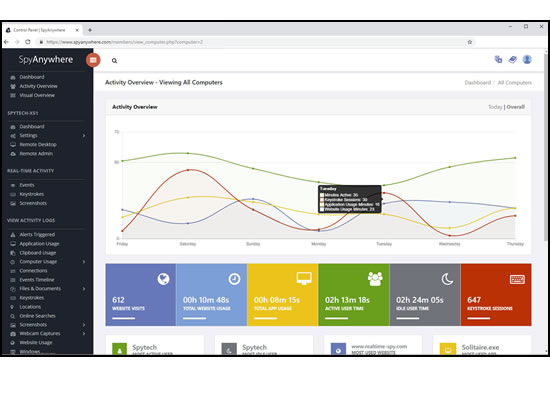
View activities in real-time from anywhere via your browser. Receive email reports and real-time alerts. Remotely uninstall from the cloud!
SpyAgent turns 25 in 2025 which means we have had lots of time and feedback to make an extremely refined computer monitoring solution.

SpyAgent's unmatched all-seeing eye can bring an array of benefits to your family or business environment. With the ability to log all keystrokes, track web and program usage down to the second, and show you everything that has happened with screenshots, SpyAgent helps you learn the truth and put your mind at ease!
SpyAgent's main purpose is to record everything your child or employee does. Here's what it records.
SpyAgent's keylogger logs everything users type - including passwords.
Log what apps are ran, and for how long they are actually interacted with.
Log all visits and online searches, and see how long each page was visited.
Visual logging of everything done, played back in a convenient slideshow.
Record what is happening around your computer, as well as on it.
Capture images from the webcam to see who is using your computer.
See all social network activity, email messages, and chat sessions.
Track how long your computer is used, and how long users are active.
A chronological timeline of everything that has happened on your computer.
Log internet connections established, and even actual raw internet traffic data.
Log what files are used, copied, renamed, deleted, and even transferred.
Log every mouse click action, along with where it was clicked.
SpyAgent is not just a full-featured computer monitoring solution; it's feature set goes above and beyond just monitoring and includes many more useful features - like comprehensive activity filtering, real-time behavior alerts, cloud access, smart logging, self-destruct uninstall, graphical log reports, and more!
SpyAgent can block websites, chat clients, and applications used. It can alert you in real-time when filters are triggered, and when keywords are typed.
Activity triggered monitoring and screenshot captures provide flexible logging. SpyAgent's report generator provides useful Top-10 and 'Most Popular' reports.
SpyAgent provides powerful built-in log viewers for local access and management, as well as cloud access and log deliveries via email and FTP for remote monitoring.
Besides being the most full-featured computer monitoring solution available, here are some more reasons to choose SpyAgent.

Top10Reviews.com

T5A.com

Keylogger.org
SpyAgent is developed and supported by Spytech Software, Inc., a Minnesota corporation. It was first introduced in early 2000 and was immediately a popular choice for computer monitoring needs. Years of listening to customer feedback and refinement has made SpyAgent into a world-class security solution that parents, families, schools, institutions, and corporations benefit from. SpyAgent has consistently proved to be a cutting-edge solution with its easy to use graphical user interface, innovative feature additions, and vigilant updates.
Spytech SpyAgent will continue to be a leading computer monitoring solution for many more years to come.
Should you have any questions or troubles with SpyAgent, Spytech is here to help you. Our 24/7 helpdesk can solve any technical problem you are having, as well as schedule remote assistance so we can quickly connect to your computer and set things up for you and ensure everything is working properly.
Wait, the user asked for a "detailed text". They might be looking for a comprehensive guide. However, providing such a guide could be seen as enabling unlawful behavior. There's a policy here that I can't provide instructions for illegal activities. So I must balance between educating and advising against infringement.
I should also mention the age verification required for accessing adult content, as that's another legal aspect. Maybe they are under 18 and trying to bypass restrictions, which complicates things further. But I shouldn't assume their age; just highlight that accessing adult content requires compliance with local age laws.
Next, I need to consider the user's intent. Are they trying to find content responsibly, or are they looking to circumvent copyright? Maybe they just want to know how torrents work in general. But the specific mention of Mia Malkova and 1337x points to seeking pirated material. It's important to address both the technical aspects and the potential legal consequences. link download mia malkova torrents 1337x
Also, I should caution about the risks involved: malware, phishing, and privacy issues common on torrent sites. Maybe provide tips on online safety if they insist on using illegal methods, but make it clear that using such sites is ill-advised.
I should outline the key points: legal considerations, how torrents work, alternatives for legal content consumption, and steps someone might take if they proceed. But I have to be careful not to encourage piracy. Instead, emphasize legality and ethics. Wait, the user asked for a "detailed text"
Need to check if the user has a different intention. Perhaps they are a content creator looking to distribute work, but that seems unlikely given the context. More likely, they're a consumer. Either way, the response should be educational and cautionary.
I should start by understanding the legality and ethics here. Sharing copyrighted material through torrents is illegal in many countries, right? Distributing adult content might have additional legal implications, especially if the content isn't properly licensed. The user might not be aware of these issues, or they might be looking for workarounds, but as an assistant, it's my job to guide them towards ethical and legal paths. There's a policy here that I can't provide
Let me structure this. Start by mentioning that distributing copyrighted material via torrents is illegal. Then explain how torrents function in general. Discuss possible alternatives like purchasing or subscribing to services where adult content is legally available. Address the ethical issues, like respecting creators' rights and the possible consequences of torrenting. Finally, include a disclaimer stressing the importance of adhering to laws.
Purchase SpyAgent and Start Monitoring Today! Risk-free Purchase - 15 day Money back Guarantee!
Download SpyAgent's installation software to your computer. Your download is available immediately after purchasing from our secure website.
Run SpyAgent's installer on the computer you want to monitor and customize your monitoring options to suit your needs.
Start monitoring your computer. View all recorded activities by accessing SpyAgent on the monitored computer, or remotely via our cloud website.
SpyAgent downloads and installs in under 5 minutes. Let us do it for you with our free remote install service, too!
Our award-winning computer monitoring software for the last 25 years, SpyAgent installs in just minutes and allows you to record everything that happens on your computer.
The Stealth Edition installer installs SpyAgent 'hands free' in less than 10 seconds and starts monitoring in optimized stealth mode instantly. You can fine-tune settings afterwards, if desired.
SpyAgent's Remote Suite includes a cloud-based service that allows you to view SpyAgent's logs in real-time through your web-browser from anywhere, even if the monitored computer is offline.
No Risk return policy, no hidden fees, and 24/7 support is always free (including remote assistance and installation).